Cybersecurity First: Why Logistics Firms Must Embrace Real-Time Monitoring in the Digital Age

Logistics companies must prioritize cybersecurity when adopting real-time monitoring in the digital era. Supply chains now depend on digital transformation, creating vast networks that connect manufacturers, suppliers, and customers worldwide. These connections increase vulnerability to cyber threats. The adoption of tracking technology via IoT devices rose from 25% to 60% over the last two years. However, 43% of logistics professionals still lack supply chain visibility. Innovative platforms like JUSDA’s JusLink provide intelligent, secure solutions that help businesses protect their operations while enabling efficient, real-time monitoring.
Key Takeaways
Logistics companies must prioritize cybersecurity to protect against increasing cyber threats as they adopt digital technologies.
Real-time monitoring enhances supply chain visibility, allowing companies to respond quickly to disruptions and improve customer satisfaction.
JUSDA's JusLink platform offers intelligent solutions that integrate with existing systems, providing secure and efficient logistics management.
Implementing best practices like employee training and advanced threat detection can significantly reduce the risk of cyber incidents.
Continuous improvement and collaboration are essential for maintaining a secure and resilient supply chain in the digital era.
Digital Transformation in Logistics

Digital transformation is changing how logistics companies operate. Companies now invest in new technology to improve efficiency and reduce costs. According to a 2023 industry report, 74% of supply chain leaders are increasing their investments in supply chain technology and innovation. This shift helps companies address inefficiencies caused by manual processes and improves customer experiences.
Real-Time Monitoring Benefits
Real-time monitoring gives logistics companies better control over their supply chains. They can track shipments from origin to destination and monitor vehicle locations at every stage. This visibility allows companies to respond quickly to delays or disruptions. For example, if a shipment faces a weather delay, managers receive instant alerts and can reroute trucks or notify customers.
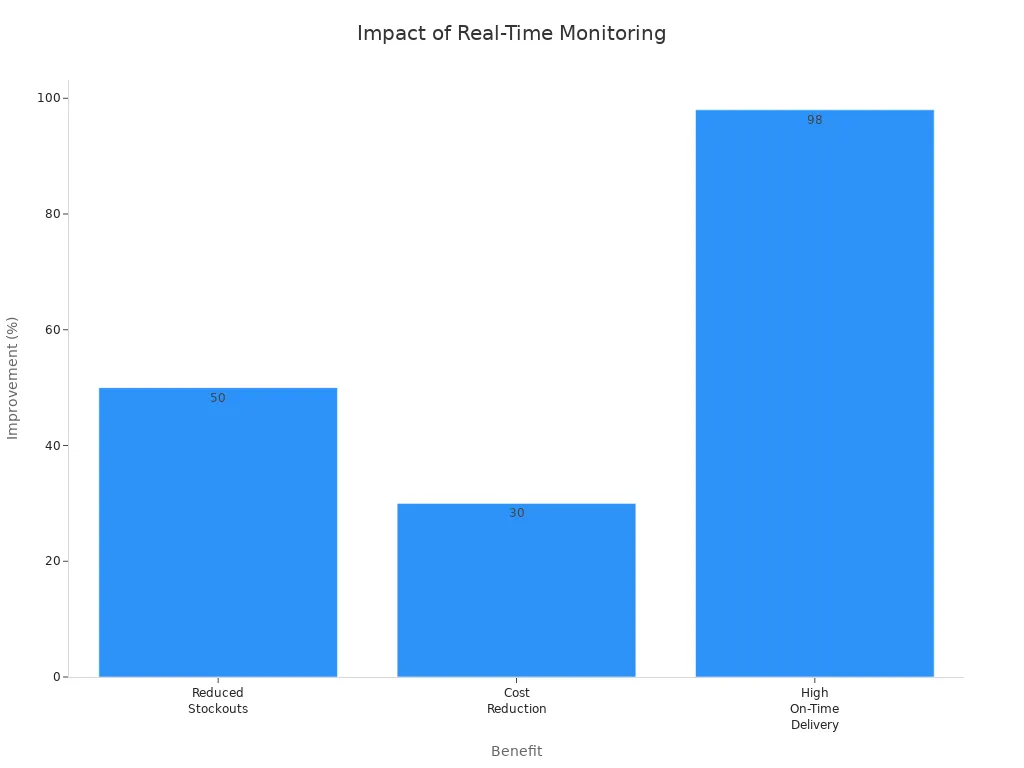
The benefits of real-time monitoring include:
Reduced stockouts by up to 50% through proactive inventory management.
Lower emergency shipping costs by 30% or more.
On-time delivery rates of 98% or higher with proactive fulfillment management.
Benefit | Description |
|---|---|
Proactive Decision-Making | Real-time data helps companies act before small issues become costly problems. |
Enhanced Collaboration | Teams share a common view of the supply chain, improving communication and strategy alignment. |
Competitive Edge | Companies respond quickly to market changes using real-time insights. |
JUSDA’s JusLink Platform
JUSDA’s JusLink platform stands out as an intelligent solution for digital transformation in logistics. JusLink integrates ERP and SAP systems with production schedules, enabling real-time logistics synchronization. The platform provides end-to-end visibility and AI-driven control, which helps companies manage risks and improve collaboration.
JusLink offers unique features:
Feature | Description |
|---|---|
Seamless Integration | Connects ERP/SAP systems with production for greater efficiency. |
Real-time Synchronization | Enables real-time tracking and management of logistics operations. |
Sky Network | Delivers a digital backbone for visibility and AI-driven supply chain control. |
JUSDA’s customer stories show that JusLink helps companies optimize processes, standardize operations, and reduce manual handling. The platform supports global expansion by providing reliable, secure, and efficient supply chain management.
Cybersecurity Threats

Common Attack Types
Logistics companies face a range of cybersecurity threats that can disrupt operations and compromise sensitive data. The most common attack types include:
Ransomware: Attackers encrypt company data and demand payment for its release. In Q2 2025, logistics companies experienced 77 ransomware incidents, making up about 12% of all ransomware activity. While this is less than the manufacturing sector, which saw 428 incidents (65% of total), logistics remains a significant target.
Data Breaches: Hackers gain unauthorized access to confidential information, exposing customer records, shipment details, and financial data.
Denial-of-Service (DoS) Attacks: Attackers flood systems with traffic, causing downtime and disrupting supply chain operations.
These threats can halt shipments, delay deliveries, and damage customer trust. As digital transformation continues, the attack surface for logistics companies grows, making robust cybersecurity essential.
IoT and Third-Party Risks
The adoption of IoT devices in logistics brings new vulnerabilities. Many devices use weak authentication, such as factory-set usernames and passwords that rarely change. Unpatched firmware leaves devices open to exploitation. Insecure communication protocols make it easier for attackers to intercept data or launch Man-in-the-Middle attacks. Vulnerabilities in third-party IoT devices can also lead to unauthorized access and data interception.
Weak authentication and default credentials have been exploited in attacks like the Mirai botnet.
Failure to patch firmware and software has led to remote code execution vulnerabilities, such as CVE-2021-28372.
Insecure communication protocols expose devices to interception and manipulation.
Third-party vendors add another layer of risk. As companies rely more on external partners, attackers exploit security gaps in these interconnected systems. By infiltrating a vendor with weak defenses, cybercriminals can access sensitive data, disrupt services, or cause data loss. Vendors may also experience supply disruptions or fail to deliver on contracts, impacting logistics operations.
Note: The interconnected nature of digital transformation means a single vulnerability can compromise the entire supply chain. Companies must assess both their own systems and those of their partners to maintain security.
Impact of Neglecting Cybersecurity
Operational Disruptions
Cyber incidents can bring logistics operations to a standstill. The UK logistics firm KNP, after 158 years in business, suffered a ransomware attack that started with a weak password. Hackers encrypted critical business data, and even after the company paid the ransom, they could not recover their files. This event forced KNP into administration and resulted in the loss of nearly 700 jobs. In July 2025, the Knights of Old Logistics Group faced a similar fate. A ransomware attack compromised their systems and backups. The company could not meet the ransom demand of £5–6 million, which led to the shutdown of operations and left around 700 employees without work. About 500 trucks became idle overnight.
Cyberattacks disrupt logistics in several ways:
Operations halt, causing immediate delays.
Financial losses accumulate quickly, with average daily disruption costs reaching $1.5 million.
Reputational damage follows, as customers lose confidence.
Attacks on one company can affect partners and customers throughout the supply chain.
A cyberattack on a major European port in 2021 disrupted cargo handling and shipping schedules. In another case, a US-based freight company lost access to its shipment tracking system due to ransomware, which caused delays and increased costs.
Financial and Reputational Damage
The financial impact of a cyber incident can devastate a logistics company. Daily losses from supply chain disruptions can range from $600,000 to $3.5 million, depending on the industry. When hackers exploit vulnerabilities, companies face not only direct costs but also long-term consequences.
Reputation suffers as well:
Delayed deliveries frustrate customers and may drive them to competitors.
Incidents of theft or delays harm a company's image and reliability.
Customer trust erodes, making it difficult to regain loyalty.
Digital transformation brings efficiency, but it also increases exposure to cyber risks. Companies that neglect cybersecurity risk losing both revenue and reputation, which can take years to rebuild.
Strategies for Secure Digital Transformation
Digital transformation in logistics brings new opportunities and risks. Companies must adopt robust cybersecurity strategies to protect their operations and maintain trust. Effective security requires a combination of advanced technology, employee awareness, and continuous improvement.
Best Practices
Logistics companies use a range of best practices to secure their digital supply chains. These practices help reduce vulnerabilities and strengthen defenses against cyber threats.
Strategy | Description |
|---|---|
Advanced Threat Detection | Uses sophisticated tools to identify and respond to threats in real time. |
Zero-Trust Architecture | Requires verification for every access request, reducing unauthorized access. |
Next-Generation Firewalls | Protects network perimeters with advanced filtering and monitoring. |
Endpoint Protection | Secures all devices connected to the network, including IoT and mobile. |
Employee Training | Builds a culture of cybersecurity awareness through regular sessions. |
Companies also implement secure API management, encryption, and continuous monitoring. They conduct comprehensive risk assessments and strengthen supplier security. Real-time monitoring and strong authentication help ensure data integrity and protect communication channels. Many organizations follow industry standards such as ISO 27001, NIST CSF, and SOC 2 to guide their cybersecurity programs.
Logistics firms using AI-driven threat detection systems have reduced their mean time to detect threats by 40%. Zero-trust architectures have lowered unauthorized access incidents by 35%.
A successful cybersecurity strategy includes:
Continuous monitoring and threat detection
Third-party risk management
Regular risk assessments and audits
Resilience through redundancy and backup plans
Staying updated on regulatory changes
Employee Training
Human error remains the leading cause of cybersecurity breaches in logistics. Studies show that 95% of incidents result from mistakes or lack of awareness. Over 90% of breaches involve social engineering, such as phishing attacks.
To address this, companies invest in comprehensive employee training programs. These programs teach staff to:
Use strong passwords and enable multi-factor authentication (MFA)
Recognize phishing attempts and suspicious emails
Stay safe when using public Wi-Fi
Keep software and devices updated
Training should start with a risk assessment and be tailored to each role. Interactive and engaging methods improve retention. Companies make training continuous and foster a security-first culture across all departments.
Regular training reduces the risk of breaches and builds a vigilant workforce. Employees who understand the risks can act as the first line of defense.
Key steps for effective employee training include:
Access management education
Ongoing training sessions
System hardening awareness
Disaster recovery planning
Technical testing and simulations
Governance and compliance adherence
JusLink’s AI Risk Management
JUSDA’s JusLink platform sets a new standard for secure digital transformation in logistics. JusLink uses AI-driven risk management to detect and respond to cyber threats in real time.
JusLink’s system provides:
Regular Cyber Risk Assessments: AI analyzes risk data quickly, highlighting urgent issues.
Consolidated Cyber Resources: AI-powered analytics unify security tools for faster, more accurate detection.
Continuous Monitoring: The platform ensures ongoing compliance and data protection.
Proactive Third-Party Risk Management: Automated monitoring tracks vendor security and flags incidents early.
Personalized Security Awareness Training: AI identifies knowledge gaps and tailors training for each employee.
Clear Incident Response Protocols: AI predicts attack patterns and recommends immediate containment actions.
JusLink’s Control Tower monitors supply chain risks and provides early warnings. The platform’s AI agents analyze international trade data, predict freight rate trends, and forecast sales demand. JusLink’s intelligent risk management helps companies respond to disruptions quickly and maintain supply chain stability.
Collaboration across departments and with external partners enhances risk visibility and speeds up incident response. A strong security culture and shared ownership reduce human errors and policy violations.
Logistics companies that use JusLink benefit from:
Real-time risk detection and alerts
Automated incident response
Improved compliance with global standards
Enhanced resilience against cyber threats
Continuous improvement and collaboration remain essential. Companies must review and update their cybersecurity strategies regularly. By leveraging JusLink’s AI-driven capabilities, logistics firms can build a secure, efficient, and future-ready supply chain.
Cybersecurity plays a vital role in the digital transformation of logistics companies. JusLink enables safe, efficient, and resilient supply chain operations through intelligent risk management and real-time monitoring. Logistics leaders should adopt proactive cybersecurity measures and leverage platforms like JusLink.
Technology integration increases exposure to cyber threats.
Digital transformation reduces costs and increases revenue, but brings cybersecurity challenges.
Robust data protection and secure systems are essential for operational integrity.
Future trends include supply chain resilience, regulatory compliance, blockchain adoption, and advanced encryption.
Leaders should invest in threat intelligence, zero trust architecture, employee training, and regular security audits.
The logistics industry will continue to evolve, with secure digital platforms shaping a future of resilient and efficient supply chains.

JUSDA Solutions
To provide you with professional solutions and quotations.
FAQ
What makes JusLink different from other supply chain platforms?
JusLink uses AI-driven forecasting, real-time risk monitoring, and customizable microservices. The platform integrates IoT, cloud computing, and big data to provide end-to-end visibility and control across the supply chain.
How does JusLink help manage cybersecurity risks?
JusLink features an intelligent risk management system. It monitors supply chain risks in real time, provides early warnings, and enables fast responses to disruptions. The platform also supports proactive third-party risk management.
Can JusLink integrate with existing ERP or SAP systems?
Yes. JusLink connects with ERP and SAP systems. This integration enables real-time logistics synchronization and improves efficiency across procurement, production, and delivery processes.
What industries benefit most from JUSDA’s solutions?
JUSDA serves electronic manufacturing, 3C home appliances, FMCG, automotive, new energy, medical health, heavy equipment, and bulk materials. The company tailors solutions to meet the unique needs of each industry.
See Also
The Importance of Logistics Security in Supply Chains
Five Key Strategies for Successful Supply Chain Cybersecurity
Top Cybersecurity Practices for Intelligent Transportation Systems