Logistics cybersecurity breaches and their impact in digital supply chain infrastructure

Cybersecurity breaches now threaten every aspect of digital infrastructure supporting logistics. In recent years, cyberattacks have halted production lines, delayed deliveries, and caused widespread disruption. The complexity of digital supply chains means a single breach can ripple across the entire network, impacting operations and customer trust.
Disruption Type | Impact on Logistics and Supply Chains |
|---|---|
Cyberattacks on key systems | Production stops, delivery delays, chaos for customers |
Weak links in supplier networks | Vulnerability spreads across the whole chain |
Companies like JUSDA and its JusLink platform use advanced technology to defend against these risks and safeguard operations.
Key Takeaways
Cybersecurity breaches can disrupt logistics operations, causing production delays and damaging customer trust.
Investing in advanced technologies like AI and IoT enhances supply chain visibility and resilience against cyber threats.
Collaboration with third-party vendors is crucial; a breach in one link can impact the entire supply chain.
Proactive measures, such as employee training and regular risk assessments, are essential for effective cybersecurity.
Using platforms like JUSDA's JusLink can improve real-time monitoring and response to potential cyber threats.
Digital Infrastructure in Modern Logistics
Key Components
Modern logistics companies rely on robust digital infrastructure to manage complex supply chains. This infrastructure supports real-time data exchange, process automation, and secure transactions. The following table outlines the main components that form the backbone of digital infrastructure in logistics:
Component | Description |
|---|---|
Internet of Things (IoT) | A network of connected devices that exchange data, providing visibility into logistics processes. |
Big Data Analytics | Tools that help extract insights from operational data, optimizing supply chains and enabling data-backed decisions. |
Machine Learning and AI | Technologies that enhance supply chain strategies, enabling research and client interactions through chatbots and remote assistants. |
Blockchain Technology | A database mechanism that allows transparent information sharing within business networks, enhancing security and transparency in logistics transactions. |
These components work together to create a digital infrastructure that improves efficiency, transparency, and security across logistics operations. Companies that invest in these technologies gain a competitive edge by streamlining workflows and reducing manual errors.
JUSDA’s JusLink Platform
JUSDA’s JusLink platform stands out as a leader in digital infrastructure for logistics. JusLink integrates advanced analytics, IoT, and AI to deliver real-time supply chain monitoring. Businesses using analytics tools like JusLink achieve up to 40% higher forecasting accuracy than their peers. The platform enables users to track shipments, assess risks, and respond quickly to disruptions.
JusLink provides real-time visibility across the entire supply chain.
The platform supports AI-driven decision-making for inventory and transportation.
Companies benefit from automated alerts and intelligent risk management.
Deloitte reports that 70% of marketing leaders now allocate budgets to AI and personalization, reflecting the growing importance of digital infrastructure.
JusLink empowers logistics teams to adapt to changing market demands and maintain operational resilience. The platform’s digital infrastructure ensures that every link in the supply chain remains connected, secure, and efficient.
Cybersecurity Threats and Impact
Common Attack Vectors
Logistics companies face a growing number of cybersecurity threats that target their digital infrastructure. Attackers use several methods to breach systems and disrupt operations. The most common attack vectors include phishing, ransomware, and supply chain attacks. These threats exploit weaknesses in both technology and human behavior.
Attack Vector | Description |
|---|---|
Phishing | Leading attack vector, worsened by AI-generated fraudulent emails. |
Ransomware | Disrupts operations by encrypting data and demanding payment. |
Supply Chain Attacks | Exploit vulnerabilities in third-party vendors to access multiple connected organizations. |
Phishing remains a top concern. Attackers send convincing emails that trick employees into revealing sensitive information or clicking malicious links. Ransomware attacks have become more frequent and damaging. Criminals encrypt company data and demand payment for its release. Supply chain attacks target trusted third parties, such as software vendors or IT providers. Hackers exploit weaker security in these partners to gain access to larger networks.
Supply chain attacks occur when hackers compromise a trusted third party.
Cybercriminals often target partners with weaker security instead of attacking a well-defended company directly.
As organizations rely more on third-party vendors, the risk of these attacks increases.
Recent studies show that software supply chain attacks have doubled. Ransomware attacks, data breaches, and IP theft now significantly impact the supply chain. Targeting suppliers increases pressure on victims to pay ransoms. In 2024, ransomware accounted for 47% of all breaches in the manufacturing sector, which includes logistics. Phishing activity in logistics reached 5.7%, and nearly 50% of phishing attempts impersonated logistics companies.
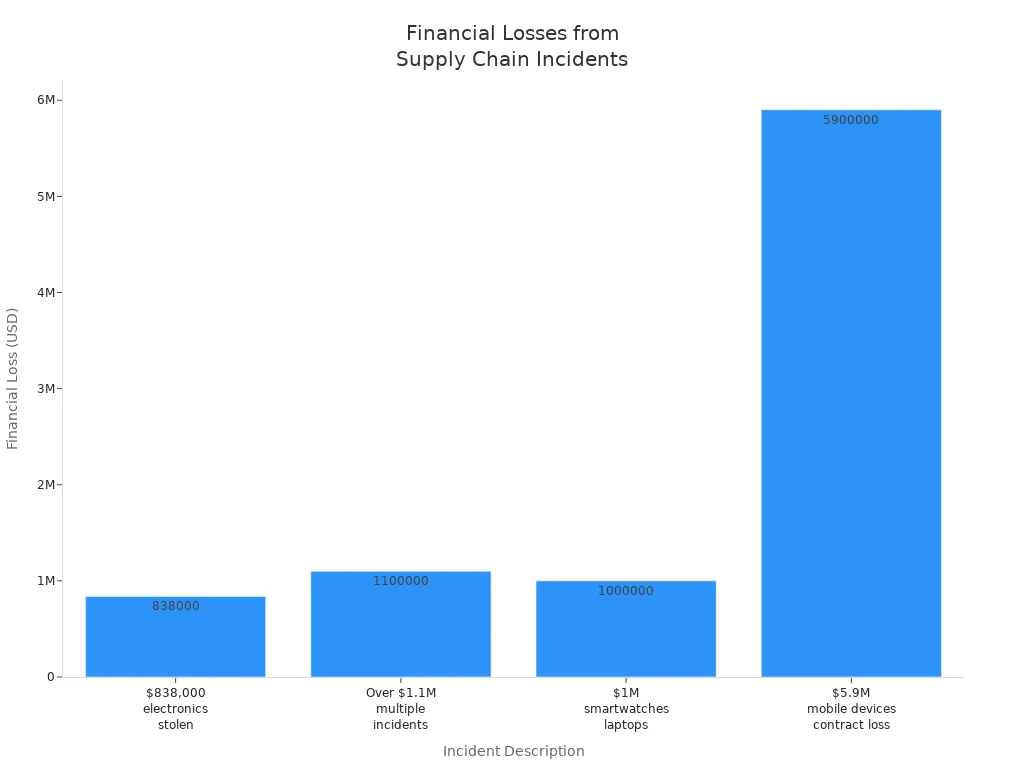
Real-World Impact on Operations
Cybersecurity issues have a direct and severe impact on logistics operations. Disruptions caused by attacks can halt production, delay shipments, and damage customer trust. The impact of disruptions often extends beyond the initial target, affecting partners and customers across the supply chain.
Some recent incidents highlight the real-world consequences of cyber threats:
Jaguar Land Rover experienced a cyber-attack that shut down car plants and impaired sales during a critical period. The attack affected dealers and repair centers worldwide, showing how interconnected logistics operations are.
In October 2023, Boeing faced a ransomware attack that disrupted its parts and distribution business. The attack led to a data leak and operational delays, exposing vulnerabilities in logistics systems.
The financial and operational losses from these breaches can be devastating.
Company | Type of Incident | Financial Loss | Operational Impact |
|---|---|---|---|
Maersk | NotPetya Attack | $300 million | Significant operational disruptions due to corrupted systems. |
Knights of Old | Ransomware Attack | £5–6 million | Forced to cease operations, 700 employees jobless, 500 trucks disabled. |
KNP Logistics | Ransomware Attack | N/A | Entered administration, struggled to find investment, 730 employees lost jobs. |
The average cost of a data breach reached $4.88 million in 2024, a 10% increase from the previous year. Nearly 40% of a breach’s total cost comes from lost customer confidence, which shows the long-term economic consequences. The impact of disruptions goes beyond immediate financial loss. Companies may lose clients, face regulatory penalties, and struggle to recover their reputation.
Regulatory requirements also shape cybersecurity strategies in logistics. Laws like CIRCIA mandate reporting of cyber incidents and data breaches. The Maritime Transportation Security Act requires cybersecurity measures for companies operating vessels or facilities. These regulations push organizations to adopt advanced threat detection, zero-trust architecture, and next-generation firewalls. Regular vulnerability assessments and endpoint protection solutions help strengthen security frameworks.
Logistics companies must address compliance challenges to avoid penalties and maintain trust with clients and partners. Adhering to cybersecurity regulations supports operational resilience and reduces the risk of disruptions. The evolving cybersecurity landscape demands constant vigilance and investment in robust security measures.
🚨 Cybersecurity threats are not just technical problems—they are business risks that can disrupt entire supply chains and critical infrastructure.
Supply Chain Interdependencies and Vulnerabilities

Third-Party Risks
Supply chain interdependencies create a network where every participant relies on others for smooth operations. This interconnectedness increases exposure to cyber threats. JUSDA’s global network demonstrates how a single weak link can affect the entire chain. JusLink’s risk management features help companies monitor and respond to threats across multiple partners.
A vendor-related cyberattack can devastate an organization: Intruders may steal sensitive data, undermine competitive advantages, disrupt operations, and incur regulatory fines.
Organizations face several risks from third-party vendors and partners:
Data breaches can expose sensitive information.
Regulatory non-compliance may result in penalties.
Reputation damage can lead to financial loss.
Operational downtime disrupts critical services.
A 2024 survey of chief information security officers found that security breaches involving third-party vendors are a top concern for public sector organizations. Major attacks often start in the supply chain, exposing businesses to risks through weak vendor security. Shared data means shared risk. A ransomware attack on a core supplier can halt operations. Regulatory frameworks require third-party risk management. Supplier breaches can lead to significant business consequences.
Complexity and Visibility Challenges
Supply chain interdependencies make it difficult to maintain visibility across all partners and processes. Organizations often lack complete knowledge of which vendors have access to their systems or data. This creates potential vulnerabilities. The complexity of supply chains leads to a web of relationships that become less visible, especially at the raw materials stage.
Projected costs of software supply chain attacks are expected to reach $60 billion by 2025 and $138 billion by 2031.
Cybersecurity is identified as the biggest threat in supply chain risk management.
Departments such as legal, operations, and IT may not communicate effectively, complicating risk management. Foreign ownership or control in the supply chain can introduce additional risks. JusLink’s Control Tower Intelligent Risk Management system provides real-time monitoring and early warnings, helping companies address visibility challenges. TPRM platforms help reduce supply chain breaches and systemic risks. They assist in meeting strict regulatory requirements and protect brand reputation by ensuring vendors maintain strong cybersecurity practices.
Supply chain interdependencies resemble a house of cards. Hackers often target smaller suppliers instead of larger organizations. By compromising one system, they can potentially bring down the entire supply chain. Companies must assess and manage risks to maintain operational resilience.
JUSDA’s Approach to Cybersecurity
JusLink’s AI-Driven Risk Management
JUSDA recognizes that cyber resilience is essential for modern logistics. The company uses JusLink, an advanced platform that leverages artificial intelligence to strengthen cybersecurity. JusLink’s AI-driven risk management system monitors supply chain activities in real time. This approach helps detect attacks such as ransomware before they can disrupt operations. The platform uses intelligent agents to analyze data, identify suspicious patterns, and flag potential threats.
JusLink’s intelligent agents provide several advantages:
They continuously monitor supply chain assets and update risk assessments.
They enhance visibility by tracking shipments and transactions in real time.
They increase security by detecting unusual activity and preventing theft or loss.
They use AI-driven threat detection to spot anomalies that may signal cyberattacks.
These features help companies respond quickly to breaches and minimize the impact of ransomware. JusLink’s Control Tower Intelligent Risk Management system sends automated alerts when it detects risks. This allows logistics teams to act before attacks escalate. The platform also supports compliance with industry regulations, reducing the risk of penalties.
JUSDA’s customer stories highlight the value of this approach. For example, a leading Chinese manufacturer faced complex global supply chain challenges. JUSDA implemented its AI-powered platform, which improved transparency and reduced manual handling. The manufacturer achieved better cyber resilience by standardizing processes and using real-time monitoring to prevent disruptions. The platform’s intelligent agents helped the company avoid costly downtime from ransomware and other attacks.
JusLink’s AI-driven risk management transforms cybersecurity from a reactive process into a proactive shield for logistics operations.
Building Resilient Digital Infrastructure
JUSDA builds resilience into every layer of its digital infrastructure. The company follows industry best practices to ensure that logistics operations can withstand attacks and recover quickly. Key elements of a resilient digital infrastructure include visibility, flexibility, adaptability, and technology integration.
Key Element | Description |
|---|---|
Visibility | Tracks shipments and assets in real time to prevent disruptions and inefficiencies. |
Flexibility | Adjusts quickly to changing demands and circumstances within the supply chain. |
Adaptability | Switches suppliers or implements alternative solutions in response to disruptions. |
Technology Integration | Uses IoT and AI for real-time data and situational awareness to enhance resilience. |
JUSDA’s infrastructure provides real-time insights into every stage of the supply chain. The company uses IoT devices and AI analytics to monitor shipments, inventory, and partner activities. This visibility helps prevent ransomware attacks from spreading and supports rapid response to breaches. Flexibility and adaptability allow JUSDA to adjust operations when attacks threaten critical systems. The company can switch suppliers or reroute shipments to maintain service.
JUSDA also emphasizes collaboration among stakeholders. The platform fosters strong relationships between logistics teams, suppliers, and customers. This collaboration supports cyber resilience by ensuring that everyone responds quickly to attacks and shares information about threats.
Building resilience requires more than technology. JUSDA develops contingency plans, diversifies suppliers, and maintains secure transportation networks. The company’s holistic approach ensures that logistics operations remain secure, even when facing sophisticated attacks or ransomware campaigns.
Cyber resilience is not a one-time project. It is a continuous process that combines technology, people, and processes to defend against evolving threats.
JUSDA’s commitment to cybersecurity and resilience positions the company as a leader in digital supply chain protection. The JusLink platform empowers logistics teams to detect attacks, respond to breaches, and maintain operational integrity in a rapidly changing threat landscape.
Best Practices for Securing Digital Supply Chains
Proactive Cybersecurity Measures
Organizations in logistics must adopt proactive cybersecurity measures to protect digital supply chains and maintain resilience. Effective business continuity depends on a layered approach to security. Companies should:
Implement proper access management using role-based controls. This limits exposure by ensuring only authorized personnel access sensitive data.
Collect and manage logs systematically. Tracking actions during incidents improves response and supports business continuity planning.
Integrate suppliers into resilience and improvement initiatives. Collaboration with partners aligns security practices and strengthens the entire network.
Design processes for monitoring the supply chain. Regular risk assessments and continuous monitoring help detect threats early and provide visibility on supply chains.
Utilize technology for real-time visibility on supply chains. Tools like IoT and AI enable continuous tracking of assets, enhancing both security and operational efficiency.
Identify vulnerabilities through penetration testing. Regular tests uncover complex threats before attackers exploit them.
Develop a robust response plan. A structured incident response plan ensures effective business continuity and rapid recovery from breaches.
Continuous monitoring remains essential. Threat intelligence integration allows organizations to track stolen data and adapt defenses. Adaptive measures, such as updating protocols after incidents, further improve resilience.
Proactive cybersecurity measures form the foundation for effective business continuity planning and operational continuity in logistics.
Collaboration and Employee Training
Resilience in digital supply chains requires more than technology. Collaboration across departments—finance, operations, and IT—ensures that cybersecurity becomes a business-wide priority. Sharing a common language about security investments helps organizations evaluate risks and make informed decisions.
Cross-company collaboration also enhances resilience. Integrating Cyber Threat Intelligence Platforms enables information sharing, even among competitors. This cooperative approach strengthens collective readiness and supports effective business continuity planning.
Employee training plays a critical role in reducing cybersecurity risks. Structured training programs equip staff to recognize and respond to threats, minimizing human error. Organizations that invest in cyber awareness training contain breaches more quickly. According to industry research, containing a breach within 200 days can save over $1 million. Training costs remain low compared to potential losses, making it a smart investment.
Strategy | Impact on Cybersecurity Risks |
|---|---|
Employee Training | Equips employees to recognize and respond to threats, reducing risk |
Strong Access Control | Prevents unauthorized access to sensitive information |
Regular Updates | Fixes known vulnerabilities in systems |
Incident Response Plan | Minimizes damage during a cybersecurity incident |
A strong security posture combines advanced tools, collective vigilance, and a culture of resilience. This approach ensures effective business continuity and protects the integrity of digital supply chains.
Cybersecurity breaches in logistics can disrupt public safety, destabilize economies, and erode trust.
Attacks often cause financial losses, production delays, and environmental harm.
Leaders prioritize risk-based investments and regular assessments to protect critical assets.
Description | |
|---|---|
Advanced Anomaly Detection | AI models identify subtle threats, enhancing security. |
Dynamic Supplier Risk Scoring | Real-time risk scores focus resources on high-risk vendors. |
Predictive Threat Intelligence | AI predicts disruptions, enabling proactive adjustments. |
Automating Compliance | NLP speeds onboarding and ensures policy compliance. |
An attack on logistics systems can halt shipments and trigger ripple effects across supply chains.
Digital supply chain security will continue to evolve as threats grow more complex. Leaders must embrace advanced solutions like JusLink and foster a culture of continuous improvement.

JUSDA Solutions
To provide you with professional solutions and quotations.
FAQ
What are the most common cybersecurity threats in logistics?
Phishing, ransomware, and supply chain attacks top the list. Attackers often target weak links in vendor networks. These threats can disrupt operations, steal data, and damage reputations.
How does JusLink help manage supply chain risks?
JusLink uses AI-driven risk management. The platform monitors supply chain activities in real time. Intelligent agents detect threats, send alerts, and help companies respond quickly to disruptions.
Why is third-party risk important in digital supply chains?
Third-party vendors often have access to critical systems. A breach at one partner can impact the entire network. Managing these risks protects operations and maintains trust.
What steps can companies take to improve logistics cybersecurity?
Companies should use strong access controls, train employees, monitor systems continuously, and develop incident response plans. Regular risk assessments and collaboration with partners also strengthen defenses.
How does AI improve supply chain security?
AI analyzes large volumes of data for unusual patterns. It predicts risks, automates alerts, and supports faster decision-making. This proactive approach helps prevent disruptions and reduces response times.
See Also
The Importance Of Logistics Security In Supply Chains
Five Key Strategies For Successful Supply Chain Cybersecurity
Understanding The Trends In Logistics Risk Management