Rising Cyber Threats Expose Deep Vulnerabilities in Global Supply Chain and Logistics Infrastructure

Cyber threats now target global supply chains and logistics infrastructure with unprecedented frequency. Recent data shows a sharp increase in incidents:
Over two-thirds of logistics industry leaders rate cybersecurity as highly relevant.
Software supply chain attacks now average 26 per month.
Ransomware incidents rose by 37% year-over-year, with 44% of breaches involving data-extortion.
Organizations face critical vulnerabilities that can disrupt operations and erode trust. Supply chain cybersecurity protects business continuity and national resilience, as even a single compromised update can impact thousands of companies.
Key Takeaways
Cyber threats are increasing, with over two-thirds of logistics leaders recognizing the importance of cybersecurity.
Organizations must assess third-party vendors rigorously to prevent breaches, as 30% of attacks involve third-party software.
Real-time monitoring and visibility are crucial for detecting threats early and maintaining supply chain integrity.
Implementing AI and digital solutions can enhance risk management and improve response times to cyber incidents.
Collaboration and information sharing among supply chain partners strengthen defenses against evolving cyber threats.
Supply Chain Vulnerabilities
Third-Party and Software Risks
Global supply chains depend on a vast network of third-party vendors and software providers. Each connection introduces new risks. JUSDA’s global network, with over 155 service points and extensive warehouse operations, demonstrates the complexity of these environments. Attackers often exploit vulnerabilities in third-party software to gain access to sensitive systems. Recent industry data shows that 30% of breaches now involve a third-party, doubling from previous years. More than 75% of organizations have experienced a software supply chain attack in the past year. The financial impact is significant, with the average cost of a data breach reaching $4.44 million globally and $10.22 million in the US.
Evidence Description | Statistic |
|---|---|
Third-Party Breaches | 30% of breaches involve a third-party (100% increase from 15%) |
Malicious Packages in Open Source | 512,847 malicious packages logged in 2024 (156% increase) |
Organizations Experiencing Attacks | More than 75% of organizations faced a software supply chain attack in the last year |
Average Cost of a Data Breach | $4.44 million globally, $10.22 million in the US |
Supply Chain Cost Premium | Average additional cost of £241,620 in the UK due to supply chain breaches |
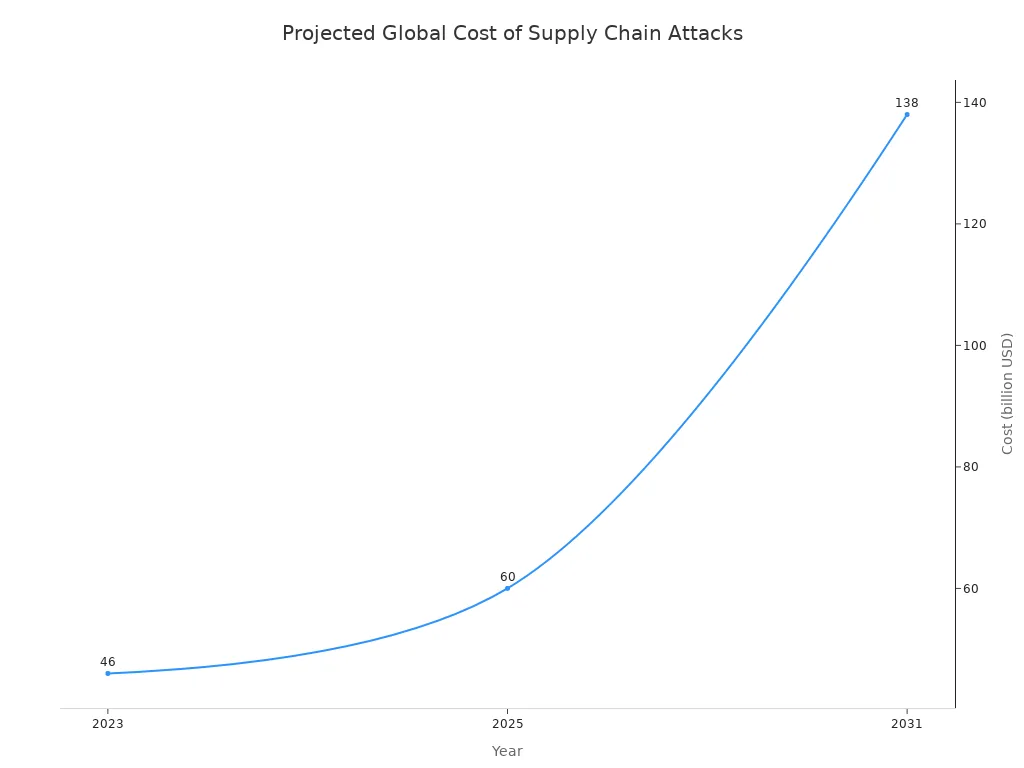
Projected Future Costs | Global annual cost of software supply chain attacks to rise from $46 billion in 2023 to $60 billion in 2025 and $138 billion by 2031 |
To address these risks, organizations should:
Perform rigorous vendor risk assessments.
Enforce strong security contracts and SLAs.
Maintain an accurate software inventory.
Implement real-time monitoring and threat intelligence.
Adopt a zero-trust approach to third-party access.
Strengthen API security.
IoT and Infrastructure Weaknesses
Modern supply chains rely on IoT devices and digital infrastructure. These technologies improve efficiency but also introduce new vulnerabilities. JUSDA’s warehouses, equipped with advanced management systems like JusLink, highlight the scale of connected devices in logistics. Common weaknesses include lack of encryption, weak authentication, physical security risks, and shadow IoT devices. These vulnerabilities can lead to unauthorized access, data breaches, and operational disruptions.
Vulnerability Type | Description |
|---|---|
Lack of Encryption | Unencrypted data transmission exposes sensitive information to interception or theft. |
Weak Authentication Mechanisms | Insufficient authentication makes devices vulnerable to unauthorized access and control. |
Physical Security Risks | Devices in public areas can be tampered with, leading to data leaks or manipulation. |
Shadow IoT Devices | Unauthorized devices can connect to networks, bypassing security measures and increasing risks. |
Attackers have exploited legacy firmware, insecure defaults, and silent exploit paths in recent incidents. These risks threaten the integrity of supply chain operations.
Limited Visibility and Interdependencies
Supply chain vulnerabilities often stem from limited visibility and complex interdependencies. Organizations struggle to oversee the security maturity of all suppliers, especially as supply chains expand. JUSDA’s integrated platforms help improve transparency, but challenges remain. The growing attack surface and interconnected systems increase the potential for attacks and damage. Enforcing security standards across all partners is difficult, particularly in less regulated industries.
Challenge | Description |
|---|---|
Limited Visibility | Organizations struggle to maintain oversight of suppliers’ security maturity due to expanding supply chains. |
System Interdependencies | The growing attack surface and interdependencies increase the potential for attacks and damage. |
Enforcement of Security Standards | Difficulty in enforcing security standards on suppliers, particularly in less regulated industries. |
Note: Addressing these vulnerabilities requires continuous monitoring, collaboration, and investment in advanced security solutions.
Impact on Critical Infrastructure
Disruption in Logistics and Transportation
Cyber vulnerabilities in logistics and transportation have a direct impact on critical infrastructure. Attacks on these sectors can halt the movement of goods, disrupt supply chains, and cause financial losses. Over the past five years, cybersecurity incidents in logistics have increased by 48%, making this one of the top three targeted sectors for threats. Maritime ransomware incidents have surged by 467% year-on-year. NATO has identified significant gaps in maritime defense, showing that both military and civilian logistics networks face risks from cyber threats. A single day of disruption can stall transport operations, making it difficult to restore visibility and costing companies revenue. Legacy IT systems, third-party suppliers, and human error all contribute to these vulnerabilities.
Regulation | |
|---|---|
CIRCIA | |
Cyber Incident Reporting Act | Mandates notification of data breaches involving information. |
Covered Entities | Includes shippers and logistics firms that must report cyber incidents. |
Real-World Breaches and Consequences
Recent breaches have shown the severe impact of cyber threats on critical infrastructure. In July 2024, a flawed software update caused a global outage, disrupting airlines, hospitals, and logistics firms. Airlines canceled thousands of flights, and hospitals postponed surgeries. The total cost of this outage exceeded $1 billion. Other notable breaches include the SolarWinds Orion attack, which compromised government agencies and Fortune 500 companies, and the Kaseya ransomware attack, which affected over 1,500 businesses worldwide. These incidents highlight how cyber vulnerabilities in third-party software can amplify disruptions across industries.
Industry-Specific Risks (e.g., Automotive, Electronics)
The automotive and electronics sectors face unique threats due to their reliance on automation and digital systems. JUSDA’s expertise in these industries shows how cyber vulnerabilities can disrupt warehouse operations and production lines. As warehouses automate, they become easier targets for attacks. Disruptions in operational technology can paralyze production, leading to lost revenue and market share. Industrial control systems and IoT devices present entry points for attackers. Over 70% of industrial manufacturers experienced a cyber incident last year, and 1 in 4 had to shut down operations. These threats put critical infrastructure at risk and can damage consumer trust.
Cybersecurity Strategies for Resilience
Enhancing Visibility and Monitoring
Organizations must prioritize visibility and monitoring to strengthen cybersecurity across the supply chain. Effective monitoring enables rapid detection of threats and supports cyber resilience. Companies should implement a Security Information and Event Management (SIEM) tool for log analysis and incident identification. Comprehensive logging at every level of the environment is essential. Maintaining an up-to-date inventory of devices and firmware helps track assets and identify vulnerabilities. Establishing a baseline of normal network behavior allows teams to detect anomalies quickly.
JUSDA’s JusLink platform and warehouse management systems provide real-time monitoring and inventory tracking. These systems enforce configuration management and alert on unauthorized changes. Monitoring external-facing devices and scrutinizing configuration changes further reduces risk. Organizations should store configurations centrally and monitor them frequently. Limiting exposure of management traffic to the Internet and monitoring user logins for anomalies are also critical steps. Secure, centralized logging with encryption and off-site storage ensures data integrity.
Technologies such as GPS, RFID, and IoT sensors enhance real-time monitoring. GPS provides accurate shipment tracking, while RFID improves inventory management. IoT sensors monitor shipment conditions, which is vital for perishable goods. Blockchain technology offers secure data sharing and transparency within the supply chain. Continuous monitoring and AI-driven analytics enable proactive identification and response to emerging threats, supporting a robust cybersecurity posture.
Tip: Establish a strong network flow monitoring solution at key ingress and egress points to detect suspicious activity early.
Vetting Third-Party Partners
Third-party partners introduce significant cybersecurity risks. Organizations must adopt rigorous vetting processes to ensure cyber resilience. Reviewing security certifications, such as SOC 2 Type II and ISO 27001, verifies a partner’s commitment to security. Implementing password policies, access controls, and multi-factor authentication strengthens user authentication. Maintaining detailed logs and retention periods supports audit readiness.
Best Practice | Description |
|---|---|
Security Certifications | Review attestation reports like SOC 2® Type II and ISO 27001. |
User Authentication | Enforce password policies and multi-factor authentication. |
Logging and Audit | Maintain system, application, and network logs with clear retention. |
Data Center Security | Ensure physical security at data hosting locations. |
Vulnerability Management | Conduct regular assessments and timely remediation. |
End-point Protection | Establish comprehensive end-point security policies. |
Data Encryption | Encrypt data at rest and in transit. |
Vendor Onboarding Process | Standardize onboarding to enforce security standards. |
Security Ratings | Monitor vendors’ security ratings in real time. |
Thoughtful Selection Process | Use due diligence and risk assessments for vendor selection. |
Contractual Standards | Set and enforce security requirements in contracts. |
Leading organizations use continuous monitoring to assess third-party cybersecurity health. They implement proactive threat mitigation and prepare incident response plans for vendor-related incidents. Structured onboarding and regular simulations help teams respond effectively to cybersecurity events. Real-time incident response capabilities ensure organizations can address threats as they arise, rather than relying on outdated assessments.
Leveraging AI and Digital Solutions (JUSDA, JusLink)
AI and digital solutions have transformed the cybersecurity landscape. JUSDA’s JusLink AI solution exemplifies advanced risk management in supply chain operations. AI analyzes vast amounts of data, enhancing risk mitigation and detection. It provides real-time alerts, enabling immediate responses to threats. AI monitors global activities, filtering out irrelevant information and focusing on critical supply chain security issues.
JusLink’s AI excels in anomaly detection, identifying hidden threats through pattern recognition. Predictive modeling supports faster, more confident decision-making. Organizations use AI to vet new suppliers and software, ensuring rapid and thorough risk analysis. Continuous monitoring of supply chain networks identifies vulnerabilities before they can be exploited. AI-powered analytics automate security assessments, strengthening overall cybersecurity.
JUSDA’s warehouse management systems leverage AI-driven predictive analytics for threat detection and monitoring. These systems identify patterns and anomalies in user behavior, such as unusual login attempts or unauthorized data access. Real-time monitoring and automated incident responses help manage suspicious activities. AI adapts its defenses based on past incidents, improving its ability to prevent new cyber threats targeting logistics operations.
Note: Integrating AI and digital solutions like JusLink enhances cyber resilience by enabling organizations to detect, respond to, and prevent threats more effectively.
Regulatory Compliance and Best Practices
Regulatory compliance forms the foundation of a strong cybersecurity strategy. Organizations must adhere to standards such as ISO 27001, NIST SP 800-53, and CMMC. Continuous monitoring helps identify and address risks proactively. Leadership commitment and regular training foster a culture of security and compliance.
Regular compliance risk assessments and gap analyses reveal weaknesses. Mapping organizational policies to regulatory controls ensures comprehensive coverage. Automating compliance processes reduces human error and improves efficiency. Maintaining documentation and audit trails supports compliance efforts. Ongoing training reduces accidental violations and strengthens cyber resilience.
Strategy | Description |
|---|---|
Continuous Monitoring | Track vendor compliance and adapt to evolving regulations. |
Collaboration with Vendors | Conduct regular assessments and audits to address compliance issues in real time. |
Preparation for Changes | Stay updated on regulatory shifts and educate teams to address issues proactively. |
Contingency Planning | Develop plans to ensure business continuity during compliance failures. |
Risk Management Platforms | Integrate with technologies to automate tasks and track regulatory adherence. |
Compliance Automation | Use AI tools to evaluate supplier adherence and assign tasks. |
Real-time Alerts | Platforms should alert stakeholders for non-compliance or breaches. |
Centralized Data Gathering | Collect and centralize vendor data for efficient compliance evaluation and reporting. |
Efficient Onboarding | Automate compliance checks and real-time alerts for seamless supplier onboarding. |
Organizations should identify key personnel for comprehensive security training. Documenting policies based on industry standards and assessing supply chain components help manage critical dependencies and risks. Vendor risk management ensures third-party compliance, further strengthening the cybersecurity landscape.
Callout: Developing and maintaining incident response plans minimizes disruptions during cybersecurity incidents and supports business continuity.
Building a Secure Supply Chain Infrastructure
Integrated Technology Platforms
A secure supply chain infrastructure relies on advanced technology platforms. JUSDA’s global warehouse and logistics network demonstrates how integrated systems can strengthen supply chain security. These platforms provide real-time tracking, which increases visibility and helps organizations respond quickly to supply chain attacks. Visibility is essential for managing supply chain interdependencies and reducing operational disruptions. Integrated platforms also use blockchain to create tamper-proof records of transactions. This transparency lowers disputes and supports trust among partners. When combined with IoT and smart contracts, these systems automate processes and improve security. Comprehensive IoT solutions address modern supply chain risks by connecting devices, managing data, and monitoring large-scale operations. This approach ensures that digital infrastructure remains resilient against supply chain attacks.
Real-Time Risk Management
Effective risk management requires real-time insights and continuous monitoring. Organizations must validate technical controls in their suppliers’ environments to prevent supply chain attacks. Automated risk scoring and benchmarking provide actionable insights for decision-makers. Continuous supplier monitoring detects security gaps before attackers exploit them. Automated assessments evaluate a supplier’s security posture before onboarding. Vendor benchmarking helps select partners with strong cybersecurity hygiene. Risk-based action plans prioritize high-risk vendors, while tracking vendor trends reveals emerging supply chain risks and supply chain interdependencies.
Practice | Description |
|---|---|
Real-Time Insights | Validates if technical controls are effectively implemented in a supplier's external environment. |
Executive Reporting | Provides automated risk scoring, benchmarking, and trend analysis for actionable insights. |
Continuous Supplier Monitoring | Ensures ongoing visibility into supplier cyber risks to detect security gaps before exploitation. |
Automated Assessments | Evaluates a supplier's external security posture with real-time analytics before onboarding. |
Vendor Benchmarking | Compares vendor security postures to help select partners with strong cybersecurity hygiene. |
Risk-Based Action Plans | Ranks findings based on severity and asset value to prioritize high-risk vendors. |
Tracking Vendor Trends | Tracks changes in vendor cyber health over time to identify trends and emerging threats. |
Collaboration Across the Ecosystem
Collaboration across the supply chain ecosystem is vital for mitigating supply chain attacks and managing supply chain interdependencies. JUSDA’s approach emphasizes communication and transparency among partners. When organizations share information and enforce strict security protocols, they can identify supply chain risks early. Detailed assessments and ongoing surveillance help maintain strong supply chain security. This collective effort builds trust and strengthens the entire infrastructure, making it more resilient to operational disruptions and supply chain attacks.
Tip: Regular collaboration and information sharing among partners can help organizations stay ahead of evolving supply chain risks and reduce the impact of operational disruptions.
Cyber threats continue to escalate, exposing deep vulnerabilities in global supply chains. Recent data breaches highlight the impact of ransomware and malicious attacks on critical infrastructure. The table below shows the growing risk:
Evidence Description | Value |
|---|---|
45% | |
Percentage of energy-sector breaches linked to software and IT providers | 67% |
Increase in successful cyber-attacks on UK utility companies in 2023 | 586% |
Only 16% of professionals feel very confident in their organization’s visibility of supply chain vulnerabilities. Proactive strategies, such as leveraging advanced data analytics, AI, and trusted partners like JUSDA, help organizations address cyber risks and prevent malicious incidents. Organizations should assess their current defenses, monitor for data breaches, and take immediate steps to secure operations. Business leaders and IT professionals must prioritize cyber resilience to protect against ransomware, malicious actors, and evolving cyber threats.

JUSDA Solutions
To provide you with professional solutions and quotations.
FAQ
What makes JUSDA’s supply chain solutions resilient against cyber attacks?
JUSDA uses integrated platforms like JusLink and advanced warehouse management systems. These tools provide real-time monitoring, predictive analytics, and automated risk management. They help organizations detect threats and respond quickly to attacks across the supply chain.
How does JusLink’s AI solution improve supply chain security?
JusLink’s AI analyzes supply chain data, predicts risks, and monitors global activities. The system identifies anomalies and provides real-time alerts. It supports decision-makers by automating security assessments and enhancing visibility throughout the chain.
Why is visibility important in supply chain cybersecurity?
Visibility allows organizations to track assets, monitor supplier security, and detect attacks early. JUSDA’s platforms offer real-time tracking and inventory management. This transparency helps prevent disruptions and strengthens the entire supply chain.
How do JUSDA’s warehouse operations support supply chain protection?
JUSDA’s warehouses use advanced management systems for inventory tracking and control. These systems enforce configuration management and alert teams to unauthorized changes. They help maintain supply chain integrity and reduce the risk of attacks.
What role does collaboration play in defending the supply chain?
Collaboration among partners improves information sharing and early detection of supply chain risks. JUSDA emphasizes communication and transparency. This approach builds trust and strengthens defenses against attacks targeting the supply chain.
See Also
Top Five Strategies To Achieve Supply Chain Cybersecurity
Understanding Risks: Protecting Your Supply Chain Effectively
Address Supply Chain Risks Now To Secure Your Business
The Importance Of Logistics Security In Supply Chain Management
Overcoming Global Supply Chain Expansion Challenges Effectively